Efficient and Effective Risk Management with KYP
Every year, the federal government allocates billions of dollars to the Medicaid and Medicare programs. A significant portion of these funds is used to reimburse healthcare providers for the services they have provided. Researchers estimate that around 10% of the Medicare and Medicaid expenditure1 is lost in frauds and abuses. A calculated guess is that 60 billion dollars were lost in 2018. These 60 billion dollars could have been better used in numerous ways. For instance, the combined monetary need of the Department of Agriculture, Department of Commerce, Department of Education, and Department of Labor2 could be met with these 60 billion dollars. 4% of the current student debt could be forgiven with these 60 billion dollars.3 The number highlights the scale of healthcare fraud and abuses and the need to implement preventive measures.
The federal and state governments are on vigil to stop this criminal activity and have framed numerous laws and founded task teams. Here is the brief overview of the fines and custodial sentences under the various prominent laws and statutes4:
| Law/Statutes | Punishments |
|---|---|
| The Health Care Fraud Statute [18 U.S.C. § 1347] | When convicted under this statute, fraudsters can be jailed for up to 10 years and required to pay criminal fines of up to $250,000. |
| The Civil Monetary Penalties Law (Section 1128A of the Social Security Act) | The penalties range from $10,000 to $50,000 per violation. |
| The Anti-Kickback Statute (Section 1128B(b) of the Social Security Act) [42 U.S.C. 1320a–7b] | Violation of the Anti-Kickback Statute may lead to exclusion from Federal health care programs. Criminal penalties for violation are a fine of up to $25,000 and imprisonment for up to 5 years. |
| Exclusion Provisions | HHS-OIG can exclude individuals from participating in federal health care programs using section 1128 of the Social Security Act. |
| The False Claims Act [31 U.S.C. § § 3729-3733] | Penalties up to $11,000 for each false claim, three times the amount the government incurred due to the false claim, and exclusion from federal healthcare program are the other provisions. Person who knowingly makes false claims can be subject to criminal prosecution and criminal fines of up to $250,000. |
What more can be done?
Today’s fraudsters are aware of the aforementioned punishments and penalties under the laws and statutes. However, the question arises whether these laws are deterrent or not? Laws, statutes, and task teams are around for centuries and again they are reactive in nature. The law enforcement agencies swing into action only after the fraud is reported. The laws come into the force only after authorities file charges on the suspect. Legal costs, convincing jury, time, all add to costs and uncertainty of recovery of money from a fraud after it has happened. Meanwhile, millions of dollars are lost and not recovered. The need of the hour is to proactively weed out unscrupulous providers who want to tap into state and federal healthcare monies.
Is there any option that can be proactively exercised by the governments in order to prevent frauds and abuses?
Answer to this million-dollar question is yes. Our company Digital Harbor (DH) has carved a path towards zero frauds and abuses with the solution-KYP (Know Your Provider). KYP is already proven as a wherewithal for various states.
KYP: The robust solution to weed out the unscrupulous
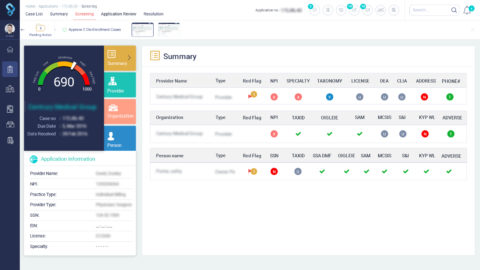
KYP, the flagship product of DH, provides out of the box capability to government agencies to screen health care providers. A question might pop up: How does KYP add efficiency to the arduous task of application processing? With its capability to function as workflow engine, data repository, collaboration tool, and intelligent application, KYP empowers application reviewers to work optimally.
Let’s understand how KYP plays each of the stated roles. Through well-defined workflows, KYP ensures that provider’s application is assigned to a reviewer within a pre-defined time frame. In case the application is not assigned or reviewed after the assignment then the alerts are sent to the concerned stakeholder. Additionally, KYP keeps track of the work done by every stakeholder and reports the status to them. With efficient workflow engine as a backbone of application processing, efficient application processing remains no longer a fiction, it becomes a reality.
As a data repository, KYP maintains accounts of healthcare providers after their applications are approved. With the data at fingertips, authorities can verify the details and run a quick fact check. However, is it easy to zero in on the unscrupulous from the applicant pool? Answer is no because a provider submits dozens of documents that need to be checked by the reviewer. Dozens of documents each with dozens of pages amount to hundreds of pages filled with information. For instance, the applicant may provide distinct addresses for his or her business and practice. Subsequently, a reviewer needs to verify different information sets. Sounds like a tricky situation, right? However, KYP provides a way out of such conundrum to users with intelligence and insights. For example, a risk score, associated with a provider, is quintessential of KYP’s capability to help application reviewers and approvers in making informed decisions.
In addition to insights and intelligence, peer knowledge and experience can help users to leverage the available data more efficiently. To this end, KYP unleashes the power of collaboration. KYP allows users to collaborate with each other through comments, messages, and chats. The information exchange through these mediums helps users in accessing the peer knowledge.
While humans work optimally, how about a help from the software? The amalgamation of human and machine intelligence? KYP brings this idea to fruition. It continuously learns from the user actions and in case of recurring event, the solution informs the user about his or her previous decision. The suggestions made by KYP helps users to quickly decide the next step and save time.
Evidently, KYP is the go to option for faster and efficient application processing. As application reviewers can leverage the power of data and collaboration with an ease, weeding out unscrupulous elements does not remain an arduous task.
Notes:
- https://www.economist.com/united-states/2014/05/31/the-272-billion-swindle
- https://www.govinfo.gov/content/pkg/BUDGET-2019-BUD/pdf/BUDGET-2019-BUD.pdf
- https://en.wikipedia.org/wiki/Student_debt
- https://www.cms.gov/Medicare-Medicaid-Coordination/Fraud-Prevention/Medicaid-Integrity-Education/Downloads/fwa-laws-resourceguide.pdf

1 Comment
Thanks for your marvelous posting! I seriously enjoyed reading it,
you may be a great author.I will always bookmark your blog and will eventually come back in the future.
I want to encourage you to ultimately continue your great posts, have a nice
afternoon!