Fraud – not just confined to Providers
Medicaid, a federal–state health-financing program for low-income and medically needy individuals, is a significant expenditure for the federal government and the states, with total federal outlays of $331 billion in fiscal year 2015. The federal watchdog Government Accountability Office estimates that about $29 billion of the payments made under Medicaid are “improper payments” which encapsulate fraud, waste and abuse of the Medicaid program.
The following categories fall under Improper payments:
- payments made for service not provided
- payments made for unnecessary services
- duplicate payments
- payments lacking supporting documents from the medical practitioner (or provider) side
- payments made to treat ineligible beneficiaries
- payments made under card sharing or identity theft
- doctor shopping which is taking multiple prescription or treatment from more than one doctor
While the number of instances of improper payments due to incorrect practices of the providers are small and involve huge dollars (millions at times), those due to incorrect practices of the beneficiaries are large but involve relatively small dollars.
Digital Harbor studied some of the real life investigation cases related to improper payments on the beneficiary side to understand the common types of fraud and the underlying reasons. Some of the cases revealed that people staying in beachside condominium and driving Aston Martins and Porches were able to bill the Medicaid program for thousands of dollars while some revealed that millions have been paid to beneficiaries who are dead, a decade back. Then there are cases of people getting Medicaid benefits from two States at the same time and there are cases of Medicaid dollars spent on people who are incarcerated for a long time.
The study pointed to the fact that applicants are able to get through Medicaid program by providing incorrect information related to eligibility criteria and also by concealing certain objectionable details about their personal and financial profile. The imposters are successfully able to use borrowed or stolen Medicaid identity details and enter the system with the primary purpose of exploiting the it by either colluding with medical practitioners or perpetrating fraudulent activities such as drug diversions and doctor shopping. Such people are also able to get enrolled to the same welfare program in more than one state and reap the benefits.
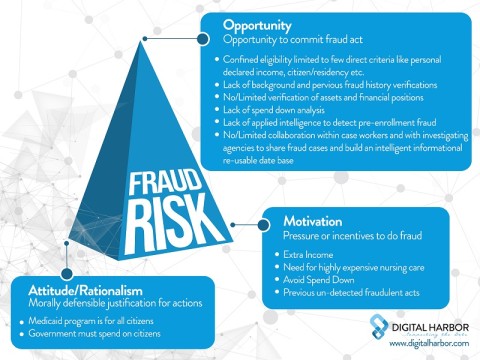
On mapping the details of our analysis to the Fraud Triangle*, we found that the ‘opportunity’ dimension was over-sized.
Opportunities to perpetrate fraud
- Entering into the system by providing false information which is not verified beyond a certain point. Lack of integrated infrastructure for verification of information such as name, social security number, address, enrolment to other welfare programs or duplicate enrolment in other state etc. from authoritative sources and inability to determine the risk of enrolling the applicant based on the mismatch of declared v/s found information are the weak links of the welfare program that makes it susceptible to manipulation.
- Lack of intelligent processes to accumulate additional information, beyond basic eligibility verification, such as job details, property ownership, beneficiary of trust, death records, prisoner records and exception listing such as Medicaid Fraud Unit, SSA (Social Security Administration), OIG (Office of Medicaid Inspector General) etc.
- Lack of regular monitoring of the applicant for changes in his/her profile which can make him/her ineligible for welfare benefits. Some events like death, prisoner, job change, change of state and duplicate enrolment with multiple states need to be monitored and the authorities should be alerted about these.
- Collaborations among case workers regarding possible knowledge of traits of fraud or being able to collaborate on a single case to share the expertise and take a collective decision.
Managing fraud needs collaboration! While some fraud does get busted at times and the government is able to recover the improper dollars paid, most of it is post-facto and a good percentage of recovery is already expensed in investigation. Overall the fall-out is clearly because of complete focus on post-factor fraud management and living by the philosophy of pay-and chase instead of deter-and-deny.
The Million-dollar question for the States is that “do you really Know Your Beneficiary?”. “Do you know the applicant as a person, as a professional, as a resident of the state and as a citizen of the country for which you are spending thousands of dollars of taxpayer’s money?”
Know Your Beneficiary, a part of Digital Harbor’s Know Your Risk suite, is a comprehensive risk-based profile of the applicant, that considers present and past information about the applicant and uses the risk events from that data to build up the risk score of the beneficiary. In short it goes qualitatively, much beyond the basic eligibility verifications and aids in informed decision making pre-enrolment and intelligent monitoring post enrolment.
